
How to Implement Age Verification on Your Website: A Step-by-Step Guide
Ensuring users are of legal age is no longer optional for many online businesses – it’s a legal requirement and a matter of trust. If your website deals with age-restricted products or content (from alcohol to adult media), regulators worldwide now expect “reasonable” age assurance, not just a simple honor-system check. Age assurance systems are a category of technology designed to confirm a user's age while addressing privacy concerns and meeting regulatory requirements across different countries. Legal requirements often specify age requirements, which are the specific age thresholds set by law or regulation for accessing certain content or services.
In this step-by-step guide, we’ll walk through why age verification matters, when it’s needed, the methods available (with pros and cons), and how to implement it in a user-friendly yet compliant way. We’ll also highlight common pitfalls and how modern solutions (like Agemin) help you achieve compliance without tanking your conversion rates.
Why Age Verification Is No Longer Optional
Online services selling age-restricted goods or content have exploded in recent years. For example, global alcohol e-commerce is projected to grow 66% between 2020 and 2025 to over $42 billion. Similar growth is seen in sectors like vaping products, online gambling, and adult entertainment platforms. As these digital markets expand, regulators worldwide have tightened the rules in 2024–2025, insisting that companies actively verify user ages. It’s no longer enough to bury an “I am over 18” checkbox on your site – governments want robust proof that minors can’t slip through.
The consequences of non-compliance are serious. Businesses face hefty fines, legal bans, and reputational damage if underage users gain access. Regulatory bodies play a crucial role in enforcing age verification laws and ensuring companies adhere to age-related regulations. In the UK, the new Online Safety Act empowers the regulator (Ofcom) to levy fines up to 10% of global turnover (or £18 million, whichever is greater) for sites that fail to implement “highly effective” age checks. The Act mandates that all service providers must use age verification or estimation to prevent children from accessing harmful content. France has gone so far as to block entire adult websites that didn’t comply with its 2024 age-verification law, leading major sites like Pornhub to voluntarily geoblock French users rather than risk penalties. In the U.S., as of 2025, 19 states (including Louisiana, Texas, Utah, and others) have enacted laws requiring strict age verification for online pornography or certain social media services. In 2026, approximately half of U.S. states will mandate age gating. Australia is drafting an Online Safety Code that would threaten non-compliant adult and gambling sites with removal from search results and social media links. Even for industries like alcohol sales, states like California and Texas explicitly mandate verifying buyer age for online orders, with penalties ranging from fines to license suspension for violators.
In short, regulators on every continent are actively enforcing age checks – ignoring these requirements can result in lawsuits, shutdowns, or loss of payment processing if your business is deemed unsafe for minors. Moreover, payment platforms and app stores increasingly have their own age-safety rules. (For instance, a Texas law will soon require app stores to verify user age for certain downloads.) The reputational hit is also significant: being known as a platform that allowed underage access can erode customer trust and invite public backlash. Robust age verification protects businesses from legal penalties, licensing issues, and reputational damage by ensuring compliance with age-related regulations.
Finally, the old “Are you over 18?” checkbox is no longer sufficient. Simple age gates that rely on the honor system have proven ineffective – minors can and do get past them by lying about their birthdate. Recognizing this, many jurisdictions now demand stronger measures. In fact, age gating (self-declaration) is considered so weak that it prompted a wave of new laws to require real verification. As one industry analysis bluntly put it, age gating mostly “depends on user honesty” and is “simple to abuse”, so companies are moving to true age verification requiring proof of age. The bottom line: if your site deals in age-restricted content, robust age verification isn’t just good practice – it’s legally and commercially essential. Regular updates to compliance practices are essential due to the rapidly shifting regulatory landscape in 2026.
When Your Website Needs Online Age Verification
How do you know if age verification applies to your site? In general, any online service involving regulated adult-only products or content should implement it. Verifying a person's age is essential to ensure compliance with legal requirements and to prevent minors from accessing restricted content. Here are clear examples of use cases that require age checks:
- Alcohol, Tobacco & Vaping Sales: If you sell alcohol, e-cigarettes, tobacco or cannabis/CBD products online, you must confirm the buyer’s legal age (18, 19, 21, etc. depending on region) before checkout. Laws explicitly extend to online vendors – for example, U.S. states mandate age verification at point of sale for alcohol e-commerce. Couriers delivering these orders also often must check ID on delivery. Skipping this puts you at risk of fines and losing your liquor license.
- Online Gaming & Gambling: Gambling websites, betting apps, fantasy sports, and even “social casinos” all typically require users to be 18+ (or 21+ in some areas). Regulations in most countries demand age verification during registration or before any wagers are placed. Likewise, video games with mature ratings or “loot box” purchases may need age gates, especially where laws ban minors from such features.
- Adult Content & Services: This includes pornography websites, erotic media platforms, adult webcam services, or even dating apps with adult content. These platforms are under heavy scrutiny. Countries like France and the UK now require stringent age verification for adult sites. If your site hosts sexually explicit content or other 18+ material, you likely need to verify age at entry (before any content is shown). Self-attestation (“I swear I’m 18”) is not considered acceptable – “reasonable age assurance” means using stronger methods to truly confirm users are adults.
- Social Media & Community Platforms: Even general platforms need to consider age checks if they have content or interactions unsuitable for children. Online platforms, including social networks, forums, or chat apps that allow user-generated content, are facing new rules to protect minors, and implementing age verification can be particularly challenging for vulnerable groups such as youth in foster care and transgender individuals. Several jurisdictions are discussing barring under-16s from social media without parental consent or requiring platforms to verify ages for accounts. For example, the UK and Australia are exploring strict age assurance for social apps, and some U.S. states (like Utah) enacted laws requiring parental consent for teens on social media. Social media accounts now often require age verification at the point of account creation to comply with these regulations and safeguard minors. If your platform has a significant number of minor users or offers content with potential harm, age verification or at least age screening is prudent to stay ahead of these regulations. Parental controls also play a crucial role by allowing parents to apply internet filters and restrictions, helping to ensure children do not access inappropriate content.
- Marketplaces with Restricted Goods: Online marketplaces that facilitate the sale of age-restricted items (for example, knives or blades, fireworks, lottery tickets, certain pharmaceuticals, or any product illegal for minors) should implement age checks for those specific categories. Even if your platform is open to all ages for general items, you need an age verification step when a user attempts to purchase a restricted product. Regulators consider it your responsibility to prevent underage transactions just as a physical store would.
In all the above cases, simply asking for date of birth or having a pop-up that “You must be 18+ to enter” is not enough. Regulators use terms like “reasonable age assurance” to mean using methods proportional to the risk – in other words, the higher the stakes (e.g. exposing a minor to pornography or gambling), the more robust your verification method should be. Age assurance can range from soft screening (for lower-risk contexts) to hard verification (e.g. government ID check for high-risk content). Document-based methods require users to upload a government-issued ID to verify their age. The UK’s Online Safety Act, for instance, calls for “highly effective” measures on any site with adult or harmful content, and has outlined acceptable methods beyond just self-declaration. The European Data Protection Board has likewise stated that any age-check technique must be minimised in data, proportionate, and auditable to count as reasonable. In practice, this means if your audience includes minors and your content is regulated, you should plan for true age verification using one of the methods in the next section.
Age Gating vs Age Verification: It’s important to distinguish these terms. Age gating usually refers to basic access restrictions like a splash page asking the user’s birthdate or a yes/no “over 18?” prompt. This is easy to implement but ultimately a low-trust barrier – users can lie, and no independent proof is required. Age verification, by contrast, means positively verifying the user's age through evidence – for example, checking a government-issued ID, analyzing a biometric (face) to estimate age, or querying a database. It offers a much higher assurance level because the user must provide something that corroborates their age. In the eyes of the law, age verification is what meets compliance standards in most scenarios above. Age gating alone is now considered a “thing of the past” in terms of protecting minors online. Many companies that once relied on age gates have upgraded to verification systems to comply with the stricter regulations. When in doubt, err on the side of implementing real age verification for any content or purchase that is 18+/21+ by law, confirming the user's age to meet legal requirements.
Types of Age Verification Methods: Including Facial Age Estimation
There are several approaches to verify a user’s age online, each with advantages and drawbacks. The best choice depends on your industry, location, risk tolerance, and user experience goals. Here’s a breakdown of the main age verification methods and when to use each:
- Self-Declaration (Age Gates): This is the classic “Enter your birthdate” or “Yes, I’m over 18” pop-up. It’s low friction and trivial to implement, causing minimal disruption to the user. However, it provides almost zero actual assurance since anyone can falsify their birthdate.
- ID-Based Verification (Document Upload): This method requires the user to submit an official ID document (like a driver's license, passport, or national ID card) to prove their date of birth. This is known as ID verification. Often combined with a “selfie” or liveness check to ensure the ID belongs to the user, it’s considered a definitive age check against authoritative sources.
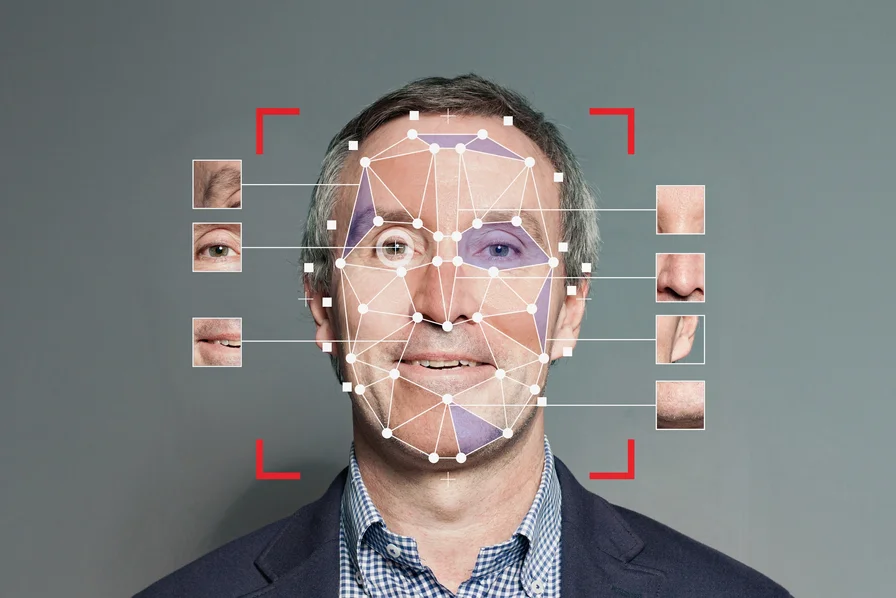
- Biometric Age Estimation: A newer, tech-driven approach is to estimate a user’s age from a live selfie or video using AI algorithms. The system uses facial analysis and machine learning to analyze the facial characteristics in a selfie to predict an exact age – typically without storing the image or personal info. Liveness detection is often used to prevent spoofing and ensure the selfie is from a real, present user. Modern facial age estimation can be quite accurate: for example, advanced models boast a mean error of only ~1–2 years in the crucial teenage range.
- Database & Credit Card Checks: These methods leverage existing data sources. For example, credit card verification uses credit card details to infer age, based on the assumption that credit card ownership implies a minimum age requirement. Similarly, some systems use public records or credit bureau data: the user enters personal details (name, address, SSN or similar) and the system cross-checks age against databases. Data sharing with third party companies and providers is often involved in these processes, which raises privacy and security concerns, including risks of data breaches and misuse. Another approach is mobile network verification– carriers often have subscriber age info (especially for contracts) and can confirm if a number is registered to an adult. It’s important to note that IP address checks are ineffective for age verification due to dynamic IP addresses.
- Hybrid Approaches (Layered Verification): In practice, the most effective strategy is often a combination of methods. A popular approach is to layer a low-friction method first, then escalate only if needed. For example, you might use a facial age estimation or database check upfront for every user. If the result comes back clearly “18+” (with high confidence), you let the user through without any further hassle. If the result is uncertain or indicates the user might be underage, then you trigger a stricter method like an ID upload. When automated methods are inconclusive, a manual review by a human reviewer may be required to check uploaded documents. Additional methods, such as analyzing behavioral signals (patterns in user behavior), can also be layered for enhanced age assurance. These hybrid flows often involve third party companies and third party providers that handle age verification and identity authentication, which introduces further privacy and security considerations.
It’s worth noting that regulators typically do not mandate one specific method – they care about outcomes (keeping minors out) and the robustness of your process.
Define Your Age Verification Requirements
Before diving into coding or vendor selection, clarify the requirements and constraints for your specific case. This will inform which solution and design make sense. Key questions to define upfront:
- Legal Age Threshold: What minimum age do you need to enforce? This depends on the product/service and jurisdiction. Common thresholds are 13 (e.g. for general internet accounts under COPPA in the U.S.), 16 (for certain social media under EU regulations), 18 (adult content, gambling, vaping in many places), or 21 (alcohol in the U.S., cannabis in some regions). You may have multiple thresholds (for instance, 18+ for some content, 21+ for other content on the same site). List out each applicable age limit.
- Applicable Laws & Regulations: Identify all countries or states where your users come from and research the age verification laws in those places. Requirements can differ widely. For example, the UK’s Online Safety Act mandates rigorous age assurance for adult content and some user-generated content platforms. The EU’s Digital Services Act (DSA) encourages platforms to use age verification as a risk mitigation for minors. Various U.S. states have their own laws for specific industries. Ensure you know if you must use a particular method (some French regulations, for instance, set standards for what counts as verifying age) or if there are reporting obligations (e.g. keeping a log of verification attempts). Also consider industry-specific rules (a gambling license might dictate age verification methods). This legal mapping will prevent surprises later and help you choose a solution that covers all bases.
By clearly defining these requirements (age threshold, where it applies, frequency, data handling, legal standards), you create a blueprint for the solution. For example, you might conclude: “We need to verify 18+ for all users in the UK before they can view content labeled adult. A one-time verification is enough per user, but it must meet the UK’s ‘highly effective’ standard. We should not store any ID images on our servers, and we need a method that works for UK and maybe EU audiences at scale.” With such specifics in mind, you’re ready to design where and how to introduce the verification in your user’s journey.
Choose Where Age Verification Happens
The point in the user flow where you enforce age checks is crucial. It affects user experience and compliance in different ways. You have a few common options for where to trigger age verification:
- Entry Gating (Before Entering the Site or Content): This means the very first thing a visitor encounters is an age check. For example, a landing page or modal that requires verification before the user can proceed to any part of the site (often used on alcohol brand websites or adult sites).
- At User Registration / Account Creation: If your service requires users to sign up or create an account, that’s a natural point to verify age. You simply build age verification into the sign-up flow. This is common for social networks, forums, or games – you don’t let an underage user even register an account.
- At Checkout or Before Transaction Completion: This approach allows users to browse and add items freely, but requires age verification when they attempt to make a purchase or perform a restricted action. It’s very common in e-commerce for alcohol or vape products: users can view products, but at checkout the site says “please verify you are over 21 to complete this order.”
- Just-In-Time (Prompted at Content/Feature Access): In this model, you only ask for age verification when the user tries to access specific age-restricted content or features. For example, a video streaming site might not age-verify every user, but if someone clicks on an R-rated movie, then it triggers a verification step. Or a social platform might allow general use but require age verification to enter an 18+ group/community.
When choosing the placement, consider the user journey and regulatory requirement together. Sometimes the law dictates it (e.g. “must verify age before allowing any access to adult content” – then your choice is made: entry gate). If not dictated, think about what makes sense for UX. A good practice is to place the verification at a natural choke-point of engagement: just before viewing sensitive content, or during the sign-up flow, or before completing an order. This way, users understand the context (“I have to do this because I’m about to do X that requires it”) rather than feeling randomly carded in the middle of browsing.
In summary, choose the point that best balances compliance and conversion. If unsure, many businesses opt for “just-in-time” at the point of purchase or access, as it weeds out minors when it really counts while keeping the funnel open for exploration. In the next step, we’ll discuss how to actually integrate the verification process technically once the point is decided.
Integrate Age Verification (Technical Overview)
Now for the hands-on part: integrating an age verification system into your website or app. The implementation can vary depending on which method and provider you choose, but there are common patterns. Here’s a high-level overview of how a typical age verification flow works and key technical decisions:
Typical Verification Flow:
- User Initiates a Restricted Action – The user either attempts to access protected content or is in a flow (signup, checkout) where an age check is required. For example, clicking “Play Video” on an adult video, or hitting “Submit Order” on an alcohol purchase, or simply arriving at your gated homepage.
- Trigger the Age Check – Your system detects that this action needs age verification. At this point, you redirect the user to an age verification process or pop-up. Technically, this could mean calling a third-party verification API, opening an SDK widget, or routing the user to a verification page on your site. For instance, you might show a modal overlay saying “Please verify your age to continue” with instructions.
- User Completes Verification – The user follows the steps of the chosen method. This could be completing a facial scan via their webcam, entering information for a database check, uploading an ID, etc. If you use a third-party service, this step might be handled by their widget or a secure mobile SDK. The aim is to capture whatever evidence is needed (selfie, ID photo, data entry) from the user and feed it into the verification system.
- Receive the Result – The verification system processes the input and returns a result to your website/app. Typically, the result could be “age verified: PASS (user is 18+)”, “FAIL (user is underage or verification failed)”, or sometimes “UNCERTAIN/REVIEW” if the system couldn’t conclude (for example, an unclear photo or a borderline age estimation might come back as needing a secondary check). The result often comes via an API response or a callback webhook to your server, or directly to the front-end if using a synchronous method.
- Grant or Deny Access – Your application logic then uses that result to decide what to do. If PASS, you allow the user to proceed with the action (e.g., complete the purchase, view the content). If FAIL, you block the action – maybe show a message “We’re sorry, we cannot allow access because age could not be confirmed.” If UNCERTAIN or NEEDS PROOF, you might trigger a fallback (e.g., ask for an ID upload if a face scan wasn’t confident). All of this should happen seamlessly so that a legitimate user can quickly continue once verified, and an underage user is stopped at the gate.
- Post-Verification Handling – After a successful verification, you’ll want to remember it. Set a flag in the user’s session or profile (e.g., age_verified=true along with a timestamp or method used). That way, the next time they hit the same gated area, you can skip directly to access if the flag is present. Also consider logging verification attempts (especially fails) for audit purposes – some regulations expect you to demonstrate your compliance efforts. Unsuccessful attempts might be logged as well, both for security (monitor if someone is trying to bypass) and for helping customers (support might get a contact from a user who failed and needs assistance).
Integration Approaches: There are two primary ways to integrate an age verification solution – API integration or Hosted/SDK integration:
- API-Based Integration: You treat the age verification service as a back-end API. Your front-end will collect necessary user input (for example, snap a photo using the device camera, or present a form for ID info) and then your server sends that data to an age verification API. The API processes it (possibly involving AI or database queries) and returns a result (pass/fail + maybe some metadata like estimated age or a confidence score). You then handle the result accordingly on your site. This approach gives you a lot of control over the user experience – you can design the UI exactly how you want, embed the process seamlessly, and just use the API under the hood. It’s great if you have development resources and want a custom flow. However, you have to do more work: dealing with file uploads (if ID images), ensuring secure data handling, making the front-end capture smooth, etc. You also need to implement any fail-safe or retries. In short, API integration = more flexibility, but more coding.
- Hosted Verification or Widget: Many age verification providers offer a hosted solution – for example, a redirect to a verification webpage, or an embeddable widget (an iframe or script) that pops up and walks the user through verification. In this case, much of the heavy lifting on UI/UX is handled by the provider’s module. You simply invoke it (e.g., include their JS, call a function verifyAge() which opens a dialog). The provider then guides the user (with screens to take a selfie or upload ID, etc.), and once done, it will notify your site of the result (often via a secure callback or by updating the parent page). Pros: Very quick to implement – often just a few lines of code and some configuration. You don’t have to worry about handling sensitive data directly; the provider does that on their side. It ensures the verification flow is consistent and tested, as it’s the provider’s own UI. Cons: Less control over the user experience styling – the widget might be branded or have limited customization. Also, the transition might not be as seamless (in case of a redirect, the user goes to another domain and back, which could be a bit jarring, though many solutions use pop-up overlays to keep it smooth). If you need a highly branded experience, hosted might not fit, but many providers allow some white-labeling or CSS customization.
In both cases, frontend vs backend responsibilities need attention. For example, if using a mobile app, you might integrate the provider’s SDK to capture a live camera feed (front-end does that), but then the backend of the provider does analysis and your backend waits for a webhook. Generally:
- The front-end is responsible for initiating the user interface for verification (camera access, file select, input forms) and pausing the user’s action until a result comes.
- The backend (yours and/or the provider’s) is responsible for securely analyzing the data and making the verification decision, as well as informing the front-end of the result. Your backend should ultimately enforce the access control. Do not rely solely on front-end flags (those can be manipulated). For example, if the front-end gets a “PASS” and then shows content, ensure that your backend also got confirmation and would not serve content to an unverified session if a clever user tries to skip the process. Tie the verification status to any API calls or page loads that deliver restricted material.
One useful tip: test the integration thoroughly in a staging environment. Simulate both pass and fail scenarios. Ensure that an underage tester truly gets blocked 100% and that an of-age tester can get through with minimal friction. Check that your logging works and that any callbacks from the provider are securely validated (you don’t want someone spoofing a “verified” message).
In the next section, we’ll focus on designing the verification experience for privacy and UX – which ties closely into how you implement it technically.
Test, Monitor, and Optimize
Launching your age verification system isn’t the end of the story. You need to continuously test, monitor, and refine it to ensure it’s effective and user-friendly over time. Here are the ongoing practices to adopt:
- Thorough Testing Before Launch: Before rolling out to real users, test the entire age verification flow in a staging environment. Simulate all scenarios:
- Test with an of-age user who should pass using each method (does a 25-year-old looking person pass the face check? Does an actual valid ID get accepted?).
- Test with an underage scenario (does a 16-year-old fail as expected? If you don’t have a real minor to test, use a lower DOB on an ID or a young-looking test photo to see if the system correctly blocks).
- Test edge cases: someone right on the boundary (e.g., exactly 18 – are they counted correctly as adult? Sometimes off-by-one errors or time zone issues with birthdates can cause mistakes), someone whose ID expires, someone who tries a second time after failing, etc.
- Ensure that the fallback flows work: if you intend to let users try again or use a different method, verify that those alternate paths trigger properly.
- Check that your session handling and gating logic is solid – for example, manually verify that without a “verified” flag, content is not accessible (even via direct URL), but with the flag it is.
- If possible, enlist a small user group or friendly testers to go through the process and give feedback on clarity and ease.
- Monitor Conversion and Drop-Off Metrics: Once live, keep an eye on analytics around the verification step. Key metrics:
- Verification Success Rate: What percentage of users who start the age check end up completing it successfully? If you see a large drop (many start but don’t finish), investigate why. It could indicate technical issues (e.g., the verification service is failing often or taking too long) or UX issues (users are abandoning due to confusion or mistrust).
- False Declines/Rejections: Monitor how often users who are actually adults get incorrectly flagged as underage or fail the process. Some signals: increased support tickets like “I’m 22 but your system says I’m not” or seeing multiple retry attempts by the same user who eventually passes with an ID. If false declines are common, you may need to adjust the threshold or switch to a more accurate method for certain demographics. For instance, maybe your face AI skews younger for a certain age group – you could lower the challenge threshold for those cases or retrain the model if possible.
- User Drop-Off Rate at Funnel: If you have a multi-step funnel (e.g., add to cart -> age verify -> payment), check the conversion rate from the step before age verify to the step after. That will quantify if the verification is causing significant abandonment. It’s expected to cause some drop-off (those who are underage or unwilling will leave), but if it’s cutting out a large chunk of legitimate customers, that’s a problem to solve (maybe by adopting a lighter method or improving messaging).
- Customer Support & Recovery: Have a plan for users who struggle with verification. Despite our best design efforts, there will be some who hit snags – maybe an older adult who isn’t tech-savvy, or someone whose legitimate ID isn’t scanning well. Make sure your support team is briefed on the age verification process so they can assist users. Provide a clear way for users to reach support from the verification screen (e.g., a “Need help?” link). For cases where a user claims the system is wrong, you might need a manual override process. This could be as simple as a support agent verifying their age via a video call or manually checking an emailed ID copy and then flagging the account as verified. Such cases should be rare, but being able to handle them will save sales and goodwill. Some platforms also implement a graceful failure: for example, if a user fails automated verification, you can say “Verification unsuccessful. You won’t be charged. Please contact support to complete your purchase.” – This at least gives them a path forward and reassurance.
- Stay Updated with Regulations: The regulatory landscape for age verification is evolving quickly. Laws can change, and new jurisdictions may introduce requirements. Assign someone on your team (compliance officer or similar) to monitor legal updates in your industry. For instance, if a country you operate in lowers or raises the age threshold, you’ll need to adjust. Or if a regulator publishes new guidelines saying method X is no longer acceptable or new method Y is encouraged, you should adapt. A concrete example: Texas’s new law for app stores or other U.S. state laws coming into effect – if relevant to you, you’d need to comply by that date. The EU might release standards around its digital identity wallet or age verification certificates; those could become best practice. Treat age verification as a continuous compliance project, not a one-time checkbox.
- Optimize and Scale: As your user base grows or changes, ensure your age verification system scales with it. If you suddenly get a surge of traffic (say a big product launch or expansion into a new country), can your verification service handle the volume? Many cloud-based providers scale automatically, but double-check any rate limits or plan caps. Nothing’s worse than turning away legit users because your verification API started throttling. If you run an in-house solution, do load testing.
- Audit and Document: Keep records of your age verification process and any changes you make. This helps in two ways: (1) Internally, you can track what’s working or not over time; (2) Externally, if a regulator ever audits your compliance, you can demonstrate how your system works, the data (anonymized) on how effective it’s been, and the improvements you’ve made. Some regulations might require annual reports or the ability to prove you are taking “reasonable measures” – having logs and stats (like “X number of users were verified, Y underage users were blocked”) can support this.
The work doesn’t stop at launch. But the good news is, with monitoring, you’ll gain valuable insights to make the process smoother and more effective. Age verification implementation is iterative: you tighten things that need tightening (to catch any who slip through) and loosen things that are too strict (if they block good customers). Over time, you’ll find the sweet spot where you’re catching essentially 100% of underage attempts while hardly impeding legitimate users.
Common Mistakes to Avoid
Even with the best intentions, there are pitfalls that businesses fall into when implementing age verification. Here are some common mistakes and misconceptions – steer clear of these to ensure your solution truly works and keeps both regulators and users happy:
- Relying on Self-Attestation Alone: Perhaps the biggest mistake (as mentioned earlier) is thinking a simple “Yes, I’m over 18” checkbox or birthdate field is enough. This won’t hold up under legal scrutiny in most places today. It’s effectively an honor system and offers no real protection. Yet some sites still use this as their only gating. Don’t be that site. If you must include a self-attestation (maybe for UI familiarity), always pair it with a real verification step. Regulators have explicitly moved away from trusting self-reported ages due to how easily kids circumvent them.
- One-Size-Fits-All Solution Globally: Using the exact same verification method and rules for all countries and all user segments can be inefficient or even non-compliant. For example, if you only use a driver’s license ID upload globally – what about countries where not everyone has a driver’s license (or where national IDs are more common)? What if local law in one country requires a government-led verification mechanism instead? Or consider cultural differences: some user bases might find a certain method too intrusive and it could hurt your adoption in that market. Avoid a rigid approach. Instead, localize and be flexible: you might use biometric verification in regions where it’s accepted, but switch to government e-ID in a country that provides a trusted digital ID system. Or adjust the age threshold per country’s law. Many modern providers allow configuration by geography (e.g., different workflows for UK vs. US users). Comply with the strictest rules where they apply, but don’t add unnecessary friction elsewhere.
- Over-Collecting Personal Data: Collecting more data than needed “just in case” is a recipe for trouble. Not only does it raise privacy red flags (and potential GDPR violations), it also increases your liability if that data is breached. For instance, if you ask every user to fill out a full identity form (name, address, etc.) when you only need their birthdate, that’s overkill. Or storing copies of everyone’s passports indefinitely – that’s a huge target for hackers and generally not necessary. Aim to verify age with minimal data retention. If using a third-party, see if they offer a tokenized result so you don’t hold raw data. Remember the principle: if you don’t have it, it can’t be stolen or misused. An academic study on online alcohol sales showed widespread inconsistency and basically highlighted the need for stricter enforcement because sellers weren’t properly verifying ages – part of that is also not maintaining good data practices. Keep only logs that prove compliance (e.g., “User X verified 18+ on 2025-08-01”) without storing the user’s actual ID details. And of course, secure whatever you do store with encryption and access controls.
- Poor UX Design that Frustrates Users: This can take many forms – a clunky interface, lack of mobile optimization, unclear instructions, or making the user jump through too many hoops. A common mistake is treating age verification as an afterthought bolt-on, resulting in a disjointed flow. For example, redirecting users to a blank-looking page with no branding can make them think it’s a scam. Or not providing feedback (“Is this thing working? Should I refresh?”) will cause users to drop. Test the UX thoroughly (as in Step 5) and polish it. Make it feel integrated with your site’s look and feel if you can. If using a third-party widget, see if you can customize styles or at least add your logo. And don’t forget error handling – if something goes wrong, give a friendly message. A bad UX not only drives away customers but could also push them towards unsafe alternatives (e.g., they find what they want on a less scrupulous site). Show that compliance can be user-friendly – this reflects well on your brand’s competence and care.
- Lack of Transparency with Users: Sometimes businesses try to slip in age verification without explanation, which can backfire. If a user suddenly is asked for personal data with no context, they may get suspicious or refuse. Always be upfront about why you’re verifying age and why it benefits them (safety, legal compliance). Also, be transparent about data handling (privacy). As noted, users appreciate knowing data won’t be stored and that it’s solely to verify age. If you fail to communicate, you’ll see more resistance and drop-off. Transparency builds trust, turning what could be seen as an annoyance into a moment of shared responsibility (“we’re doing this to keep our community safe”).
Building Age-Safe Digital Experiences for Age Restricted Content
Implementing age verification is about more than just checking a legal box – it’s about fostering a safer digital environment and trust with your users. In an era of increasing awareness around child safety online, getting age verification right is part of being a responsible platform. When users (and parents, and regulators) see that you take age restrictions seriously and handle them in a privacy-conscious way, it enhances your brand’s credibility. You’re showing that growth doesn’t come at the expense of safety.
The takeaway is that technology is on our side here. By choosing a flexible, modern age verification solution, you can adapt to different methods, scale easily, and update as laws change, all without reinventing the wheel. Many solutions offer SDKs and APIs that are developer-friendly so integration doesn’t become a months-long project but rather a quick add-on.
Remember, compliance and user experience are not mutually exclusive. With thoughtful implementation, you can achieve both: keep the regulators happy and keep your conversion rates healthy. Here’s to creating a safer online ecosystem, one verified user at a time.
Understanding Age Restricted Content
Age restricted content encompasses any material that is legally or ethically deemed unsuitable for individuals below a certain age, typically due to mature, explicit, or potentially harmful themes. This includes a wide range of online content, such as pornographic websites, violent or mature-rated video games, and certain features or communities on social media platforms that host age restricted material. The legal age threshold for accessing such content varies by jurisdiction and type of material, but the underlying goal is always to prevent minors from exposure to content that could be inappropriate or harmful.
To enforce these restrictions, websites and online services increasingly rely on robust age verification systems. These systems use a variety of age assurance methods to confirm a user’s age before granting access to age restricted content. Common approaches include facial age estimation—where AI analyzes facial features to estimate a person’s age—alongside checks of government issued IDs and other official documents. The Age Verification Providers Association plays a pivotal role in setting standards and best practices for these systems, ensuring that age assurance technology is both effective and privacy-conscious. By implementing these measures, businesses can demonstrate their commitment to protecting minors and complying with legal requirements, while also maintaining user trust in online spaces.
Benefits of Age Verification
Implementing age verification systems offers significant advantages for both businesses and their users. First and foremost, age verification helps protect children and young users from exposure to age restricted content, such as adult content, online gambling, or the purchase of age restricted products. This not only supports a safer online environment but also aligns with ethical business practices and social responsibility.
From a compliance perspective, robust age verification is essential for meeting regulatory requirements and avoiding legal penalties. By restricting access to certain age groups, businesses can prevent underage users from accessing services or products that are not appropriate for their age, reducing the risk of fines, lawsuits, or reputational harm. Furthermore, demonstrating a proactive approach to age verification builds trust with customers, showing that the company values user safety and is committed to responsible online conduct.
Age verification also benefits businesses by helping to ensure compliance with industry standards and government regulations, which is increasingly important as laws evolve. By preventing minors from accessing online gambling, adult content, or other restricted services, companies can reduce the risk of addiction, exploitation, or other negative outcomes for vulnerable users. Ultimately, age verification systems are a key tool for creating a secure, trustworthy, and compliant digital experience for all users.
Facial Recognition Technology
Facial recognition technology has become a cornerstone of modern age verification systems, offering a fast and user-friendly way to estimate a person’s age online. Using advanced facial age estimation algorithms, these systems analyze facial features—such as skin texture, bone structure, and other biometric markers—to provide an accurate age estimation without requiring users to submit additional documents. This approach can streamline the verification process, making it less intrusive and more accessible for users.
However, the use of facial recognition in age verification also brings important considerations around data security and privacy. Because facial images and biometric data are classified as sensitive personal information, age verification providers must implement strong security measures, including encryption and strict access controls, to protect user data from unauthorized access or breaches. Additionally, to ensure fairness and accuracy, these systems should be regularly updated and tested to minimize bias, particularly for users from diverse racial and ethnic backgrounds. By prioritizing both security and inclusivity, facial recognition-based age verification can offer a reliable and privacy-conscious solution for businesses seeking to comply with age restrictions online.
Challenges of Age Verification
While age verification is essential for protecting minors and ensuring compliance, it also presents several challenges for businesses and users alike. One of the primary concerns is the need to collect and process sensitive personal information, such as government issued IDs or biometric data, which raises significant privacy and data security issues. Users may be hesitant to share sensitive data online, and businesses must take extra precautions to safeguard this information against hacking, unauthorized access, or data breaches.
Another challenge is ensuring that age verification systems are both accurate and effective at preventing minors from accessing age restricted content, without creating unnecessary barriers for legitimate users. Determined individuals may attempt to circumvent verification methods, highlighting the need for ongoing updates and improvements to these systems. Additionally, there is a delicate balance to strike between protecting children and respecting free speech rights; overly restrictive systems can inadvertently limit lawful access for adults.
Advocacy groups like the Electronic Frontier Foundation have raised concerns about the potential risks associated with age verification, including the collection and storage of sensitive data and the impact on user privacy. To address these challenges, businesses must choose age verification solutions that minimize data collection, prioritize security, and are transparent about how user information is handled. Regular audits and updates are also essential to maintain the integrity and effectiveness of age verification systems in an evolving digital landscape.
Conclusion
The key point is that technology works in our favor. By selecting a flexible, state-of-the-art age verification solution, you can easily adapt to various methods, scale efficiently, and stay current with evolving laws—all without starting from scratch. Many providers offer developer-friendly SDKs and APIs, making integration a quick and straightforward process rather than a lengthy project.
In the end, implementing age verification should be part of your platform’s broader trust and safety commitment. Just as you invest in fraud prevention or content moderation, age assurance is becoming an essential element of responsibly managing a digital business. When done correctly, it safeguards your company from legal risks and protects your community from harm, while ensuring legitimate users can access your services without hassle.
Want to learn more?
Explore our other articles and stay up to date with the latest in age verification and compliance.
Browse all articles