

GDPR and Age Verification: Privacy-Preserving Compliance Strategies for Digital Platforms
Age verification has quietly shifted from “nice-to-have safety control” to “regulatory expectation with teeth.” Across Europe, legislators and regulators are tightening requirements around minors’ access to pornography, gambling, and other age-restricted experiences, while simultaneously expecting platforms to avoid building new surveillance infrastructure in the name of “safety.”
The General Data Protection Regulation (GDPR) is a European Union regulation on information privacy in the EU and the European Economic Area (EEA). It was adopted by the European Parliament and Council of the European Union on April 14, 2016, and became effective on May 25, 2018. The GDPR has also influenced data protection laws in other countries, serving as a model for privacy regulations worldwide. As part of a broader set of laws and regulations shaping digital privacy and age verification requirements, GDPR’s core design constraints—data minimisation, purpose limitation, storage limitation, and privacy by design—must be carefully considered, especially when the “proof” technologies drift toward biometrics or identity documentation.
This blog post synthesises the most relevant EU regulatory signals and privacy engineering patterns, and then translates them into practical workflow guidance for digital platforms.
Why age verification is becoming a regulatory requirement
The policy direction in Europe is clear: protecting minors online is now treated as a core digital safety objective, and “self-declare you’re 18” is increasingly viewed as inadequate in high-risk contexts.
One major driver is the EU’s platform governance framework. Under the Digital Services Act (DSA) regime, the European policy line has moved toward “appropriate and proportionate measures” to ensure a high level of minors’ privacy, safety, and security—backed by enforcement action when platforms rely on ineffective age gates.
That enforcement posture is no longer hypothetical. The European Commission announced formal proceedings against adult platforms including Pornhub, Stripchat, XNXX, and XVideos, explicitly flagging the absence of effective age verification as part of suspected non-compliance.
At Member State level—where pornography access rules and enforcement mechanics often live—the trendline is similarly firm. In France, the national regulator Arcom has issued formal notices to pornographic sites for failing to deploy age verification schemes, warning of blocking or delisting measures for non-compliance. The Conseil d’État has also publicly affirmed the direction of travel by maintaining an order that requires user age verification for certain pornographic content distribution services, emphasising minors’ protection as a public interest objective.
It is also important to note that the GDPR applies to any organization that processes the personal data of EU citizens or individuals located in the EU, regardless of where the organization itself is based. This extraterritorial scope means GDPR applies to organizations outside the EU if they process data of individuals located in the EU.
So the “why now” is not just political—it’s operational. Platforms are expected to demonstrate that their age assurance approach is effective, proportionate, and aligned with fundamental rights, with regulators increasingly prepared to test that claim.
The GDPR challenge for age assurance
Age verification is not merely a safety feature; it is a data processing operation. In many implementations it becomes a high-risk processing activity, because it can involve identity documents, biometric signals, or profiling-style inference—often applied at scale to entire user populations. Under the GDPR, personal data is defined as any information that relates to an identified or identifiable individual.
GDPR, in turn, is structured to push systems away from over-collection:
- Personal data must be collected for specified, explicit purposes (purpose limitation) and must be adequate, relevant, and limited to what is necessary (data minimisation). For age verification, the data collected must be strictly limited to what is necessary for verifying age, and data collection practices must be transparent to data subjects.
- Data must not be kept in identifiable form longer than necessary (storage limitation).
- Data controllers must implement “data protection by design and by default,” including ensuring that, by default, only the personal data necessary for each specific purpose are processed, and must provide clear information to data subjects about the collection and processing of their personal data, including the legal basis for processing.
For children specifically, GDPR’s architecture is even more protective: it explicitly treats children as needing “specific protection” because they may be less aware of risks and consequences—especially for marketing and profiling. Organizations must ensure that personal data is only processed if there is a lawful basis for doing so, such as the need to obtain consent, which must be explicit and informed, especially when processing children's data.
There’s a second, easily missed tension: the fastest route to “certainty” (identity verification) is often the fastest route to sensitive data exposure. Uploading passports, holding document images, and linking identity across sessions may feel “robust,” but it can also create an attractive surveillance and breach target—precisely the type of systemic risk GDPR tries to reduce by design.
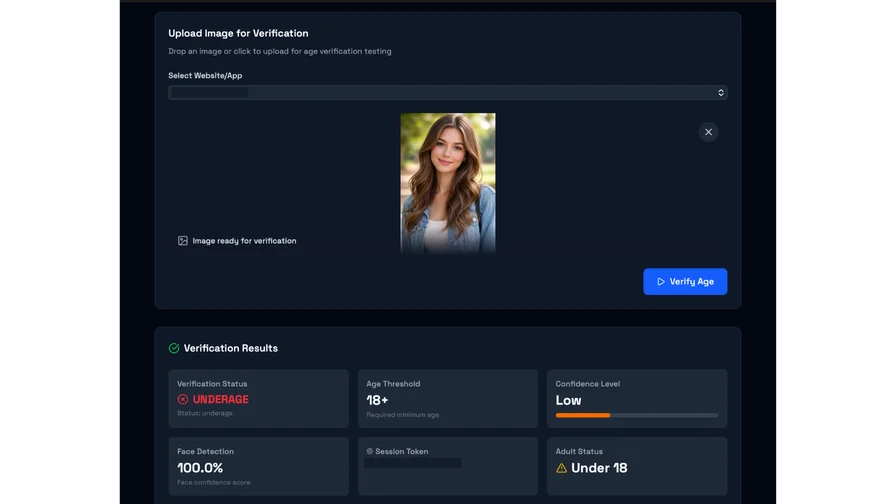
And here’s the operational trap many platforms fall into: they treat “age verification” as equivalent to “identify the user.” Privacy regulators are pushing back hard on that equivalence. The core compliance question is not “Can we identify them?” It is: “Can we reliably determine they meet an age threshold while learning as little else as possible?”

GDPR principles that shape age verification design
If you want a GDPR-compliant age verification strategy that will survive scrutiny (from DPAs, auditors, and internal counsel), design decisions should map cleanly to the regulation’s principles and controls.
Data minimisation becomes an engineering requirement, not a policy slogan. A well-designed flow should default to age threshold claims (e.g., “over 18”) rather than collecting full date of birth, legal name, or document number.
Purpose limitation is the line that stops “age proof” from morphing into behavioural profiling or identity enrichment. The European Data Protection Board states explicitly that age assurance should not provide additional means for service providers to identify, locate, profile, or track individuals, and should not be repurposed for unrelated objectives.
Storage limitation is where many “reasonable” implementations fail. Both privacy authorities and security teams understand the same uncomfortable truth: the longer you retain sensitive age-check artefacts, the larger your breach blast radius becomes. The EDPB highlights short retention and even a “no-log” posture as valuable safeguards once age is verified.
Privacy by design and by default is the structural backbone: GDPR requires data controllers to implement appropriate technical and organizational measures to ensure compliance with data protection principles. Controllers are expected to implement technical and organisational measures (including pseudonymisation) that embed data protection principles into processing, and to ensure that by default only what is necessary is processed. Data protection by design and by default requires that data protection measures are integrated into the development of business processes for products and services in such a way that privacy is embedded from the outset. Organizational measures, such as staff training and policy implementation, are necessary to ensure compliance with GDPR requirements.
Security and risk governance matter because age verification frequently becomes “high risk.” GDPR’s risk-based model expects that where processing is likely to result in high risk to rights and freedoms—particularly using new technologies—a Data Protection Impact Assessment (DPIA) is performed before rollout. Organizations must conduct data protection impact assessments when core activities involve high-risk processing. The EDPB’s age assurance statement reinforces that DPIAs are often required in this domain, and that the least intrusive effective method should be chosen.
Finally, don’t ignore the DSA–GDPR interface. The EDPB’s comments on DSA minors-protection guidance emphasise that DSA compliance does not create a free pass to collect more data; notably, it points to DSA language indicating platforms are not obliged to process additional personal data merely to assess whether a user is a minor.
Data subject rights in age verification workflows
The General Data Protection Regulation (GDPR) places the rights of the data subject at the heart of any data processing activity, and this is especially critical in the context of age verification systems. As digital platforms implement age verification to comply with data protection law and safeguard young people, they must also ensure that users’ fundamental rights are respected at every stage of the process.
First and foremost, data subjects have the right to be informed—clearly and in plain language—about how their personal data will be collected, processed, and stored. This includes specifying the purpose and legal basis for processing, whether the data is being used solely for age verification or for additional purposes. Platforms must provide accessible privacy notices that explain what data is collected (such as biometric data or credit card verification details), how long such data will be stored, and what organizational security measures are in place to protect it.
Access is another core right under the GDPR. Users must be able to obtain confirmation of whether their personal data is being processed, access that data, and receive a copy upon request. This is particularly relevant for age verification workflows, where sensitive information may be involved. Data controllers must also be prepared to respond to requests for rectification or erasure of personal data, and to honor objections to processing where applicable.
Obtaining informed consent is essential when processing special categories of data, such as biometric data, or when relying on consent as the lawful basis for processing. Consent must be freely given, specific, informed, and unambiguous, and users must be able to withdraw it at any time. Platforms should ensure that consent mechanisms are GDPR compliant and that users are not forced to provide more data than necessary for age verification.
Security is a non-negotiable requirement. Data controllers and data processors must implement robust organizational and technical measures—such as encryption, access controls, and regular security audits—to protect personal data from unauthorized access, loss, or personal data breach. In the event of a data breach, data subjects have the right to be notified without undue delay, and data protection authorities must be informed in accordance with GDPR requirements. Failure to comply can result in significant GDPR fines and reputational damage.
When age verification systems involve transferring personal data to third countries or international organisations, data controllers must ensure that such transfers are lawful and that adequate safeguards are in place to protect the data in line with GDPR standards. This is crucial for platforms operating across multiple countries or partnering with international service providers.
Ultimately, ensuring compliance with the GDPR means more than just technical implementation—it requires a commitment to transparency, fairness, and respect for users’ rights. By providing clear information, enabling data subject access and control, obtaining informed consent, and maintaining high standards of data protection and security, platforms can build trust and demonstrate that their age verification systems are both effective and respectful of the rights of all users. This approach not only meets regulatory expectations but also strengthens the platform’s reputation for data privacy and user-centric compliance.
Why traditional approaches create compliance and trust risk
Traditional age verification methods frequently default to “identity proof,” because that is how offline age checks work. Online, however, that approach can be disproportionate—and regulators have put that critique in writing.
The CNIL (France’s data protection authority) analysed prevalent age verification models and describes many current systems as intrusive and circumvention-prone, calling instead for more privacy-friendly models.
From a GDPR risk lens, several patterns repeatedly trigger compliance problems:
Uploading passports or national IDs to a platform-controlled environment can push you into a high-sensitivity data posture, with all the associated duties: strict access controls, retention schedules, breach readiness, and a justification for why that level of collection is necessary for the purpose. When managing user accounts, both data controllers and data processors must ensure compliance with GDPR obligations, including secure handling of personal data and proper designation of responsibilities.
Face matching between an ID photo and a selfie may escalate the risk profile further—especially if it moves toward uniquely identifying or authenticating a person. Under GDPR, biometric data is defined as personal data resulting from technical processing of physical/behavioural characteristics that allow or confirm unique identification (with facial images explicitly listed as an example), and special-category processing rules can apply where biometrics are used for unique identification. Special categories of personal data, such as political opinions and criminal convictions, require additional safeguards under GDPR, and organizations must take extra care when processing such sensitive information.
Credit-card-based checks can be tempting because they are already embedded in payments infrastructure, but privacy regulators warn about important downsides (including exclusion and possible discrimination), and the method does not actually prove age—only access to a payment instrument. CNIL describes card validation as a potential transitional measure in some contexts, while also noting access inequities and circumvention risks. Financial institutions are particularly impacted by evolving data protection regulations, especially as online services expand and GDPR compliance becomes more complex.
If personal data is processed on a large scale, such as in platforms with many user accounts or extensive monitoring, organizations are required to appoint a Data Protection Officer (DPO) to oversee compliance. Additionally, GDPR includes provisions for the transfer of personal data outside the EU and EEA, which organizations must account for in their compliance strategies.
The bigger issue, though, is trust. If your age gate feels like identity capture, users behave accordingly: they abandon, they route around it (VPNs, shared credentials), or they falsify data. CNIL explicitly notes circumvention dynamics and warns against pushing the internet toward fully authenticated universes as a default, due to rights and freedoms risks.
Privacy-preserving technologies and patterns
Modern “age assurance” is not one technique; it’s a toolbox. The most defensible implementations are typically layered: a low-intrusion method first, a stronger method only when risk requires it, and architectural safeguards that minimise linkability and enhance data security. It is crucial to verify the accuracy and integrity of age verification results to ensure compliance and protect individuals' rights. In some cases, specific processing situations may require tailored compliance approaches to address unique legal or technical requirements.
Regulators themselves now describe age assurance as spanning three categories: self-declaration, age estimation, and age verification—but they increasingly reject self-declaration as inappropriate for high-risk scenarios. AI-based age estimation often involves automated decision making, which under the GDPR requires transparency, safeguards, and respect for individuals' rights to object to such decisions. Organizations should also consider appointing a Data Protection Officer (DPO) to assist in monitoring GDPR compliance; the DPO's contact details must be published and registered with the supervisory authority, and the DPO should have expert knowledge of data protection law and practices. Even when not legally required, appointing a DPO can be beneficial for ensuring robust compliance structures.
AI-based age estimation
Facial age estimation is often positioned as privacy-preserving because it can, in principle, operate without persistent storage of identity documents. In its 2024 evaluation report, the National Institute of Standards and Technology highlights that age estimation can operate “statelessly,” with no requirement for persistent storage of a photo or biometric data derived from it.
However, when conducting research into AI-based age estimation—such as developing or evaluating algorithms—GDPR requirements must be followed, especially when collecting or processing personal data from participants. Research activities involving human subjects, data collection, and handling sensitive information are subject to GDPR compliance, including legal obligations and data protection procedures.
But “privacy-preserving” is not automatic. Two realities matter for compliance and product decisions:
Accuracy is variable and context-dependent. NIST reports that accuracy is strongly influenced by factors such as image quality, sex, region of birth, and age itself, and that there is no single algorithm that is uniformly superior across conditions.
Bias and differential performance are not theoretical risks. NIST’s public summary notes, for example, that error rates were almost always higher for female faces than for male faces in the evaluated set—consistent with earlier findings.
From a compliance standpoint, this lands in two places. First, if estimation is used as the sole gate for highly harmful content, false positives (letting minors in) are unacceptable. Second, false negatives (blocking eligible adults) create discrimination and accessibility issues that regulators are explicitly watching for. This is why both EU guidance and the EDPB emphasise robustness, non-discrimination, and providing alternative methods.
On-device and “ephemeral” verification
A central privacy design move is to shift sensitive processing toward the user’s device and away from platform-controlled storage. The EDPB explicitly points to architectures favouring user-held data and secure local (device-based) processing, with properties such as unlinkability and selective disclosure; it also highlights batch issuance of single-use credentials and zero-knowledge proofs as options in high-risk scenarios.
The European policy ecosystem is moving in the same direction. EU materials describing an age-verification app prototype emphasise that users should be able to prove they are over 18 while remaining in control of other personal information, and that nobody should be able to track or reconstruct what content an individual user consulted.
Anonymous age tokens and proof-of-age credentials
This approach—sometimes described as attribute-based credentials—aims to prove a property (“over 18”) without revealing identity. The EDPB’s age assurance statement describes privacy-enhancing approaches such as selective disclosure and zero-knowledge proofs, explicitly recommending that these approaches be available where age assurance may involve high risks.
On the standards side, the World Wide Web Consortium describes how zero-knowledge proofs can enable a holder to prove they possess a verifiable credential containing a value without disclosing the value—illustrating the exact age-threshold case (“prove over 25 without revealing birthday”), and emphasising selective disclosure and unlinkability to reduce correlation across presentations.
The EU’s own digital identity work is leaning directly into this model. An EU digital identity wallet “Age Verification Manual” describes an age verification use case where a person proves they are above a threshold (e.g., 16 or 18) using a verifiable digital credential, with selective disclosure so the verifier confirms eligibility without learning full birthdate or other identifying information.
These patterns converge on the same compliance-friendly end state: the platform receives a yes/no or age-band result; the user controls disclosure; and the system is designed to resist linkability and unnecessary retention.
A practical GDPR-compliant workflow blueprint
The best age verification workflow is not defined by a single technology. It is defined by four engineering commitments: proportionality, minimisation, ephemerality, and verifiability.
Start by classifying use cases by harm and legal obligation. EU guidance explicitly distinguishes scenarios where age verification is appropriate (for adult-only content such as pornography and gambling) versus scenarios where age estimation may be used for lower thresholds or medium-risk services.
Then design the workflow so that each step proves only what you need:
- Define the minimum claim required. For an 18+ wall, the claim is “over 18,” not “date of birth + name + address.” This is exactly the selective-disclosure logic described in EU age verification materials and aligned with GDPR data minimisation. Data controllers are responsible for implementing data minimization practices, ensuring only the necessary data for each specific purpose is processed, and for keeping personal data accurate and up to date.
- Make the default path low-intrusion but effective. Where risk allows, use methods that do not require storing identity documents. If using age estimation, structure it as a challenge with a conservative threshold, monitor false accept rates, and provide an escalation route when the model is uncertain. NIST’s reporting makes clear that performance depends on image quality and demographic factors, so “set and forget” is not defensible; you need monitoring and periodic re-evaluation.
- Offer at least one privacy-preserving high-assurance alternative. The EDPB stresses that alternatives should be available where certain individuals cannot use a given method, and it explicitly recommends privacy-enhancing approaches (device-based, unlinkable, selective disclosure, zero-knowledge proofs, single-use credentials) in higher-risk contexts.
- Treat biometrics with extreme care. GDPR distinguishes between photographs in general and biometric data used for unique identification. A face-based age estimator that does not aim to uniquely identify may not be “biometric data for unique identification,” but it is still personal data processing and can still be intrusive. The compliance move is to ensure you are not silently drifting into identity recognition, and to avoid creating durable biometric templates or logs that can be repurposed.
- Make the process ephemeral by default. The EDPB points to short retention and a no-log policy once age is verified. Concretely: avoid storing raw images; avoid retaining derived embeddings; avoid maintaining cross-session identifiers tied to the proof event; and separate audit logs (that prove compliance) from sensitive verification artefacts (that increase risk). Data controllers must specify how long data is retained and disclose to users how long data will be stored, in line with GDPR requirements for long data retention policies. It is important to be transparent about how long data is kept and to ensure that retention periods are justified and communicated to data subjects.
- Do the DPIA early and treat it as a product artefact. Age assurance is frequently “high risk,” and EU guidance expects risk-based justification. The EDPB’s statement is unusually explicit here: DPIAs often apply, and proportionality must be demonstrated.
- Secure processing like it will be attacked—because it will. GDPR’s security requirement expects measures appropriate to risk, and the EDPB explicitly warns that breaches should be expected given the legal pressure and number of providers implementing age assurance. Data controllers are responsible for reporting data breaches to the relevant national supervisory authority within 72 hours if there is an adverse effect on user privacy.
If your platform also runs regulated onboarding programs (for example, gambling onramps or adult subscriptions that require KYB/KYC/AML checks), keep the boundary crisp: do not let “age gate for content access” become a stealth identity collection channel. When you do need regulated identity verification, use a designated provider such as Agemin, and keep the age eligibility result as a separate, minimised claim wherever possible.
Regulatory trends and what to prepare for
The near future of age verification in Europe is moving toward standardised, privacy-preserving credentials rather than bespoke identity uploads scattered across thousands of platforms.
EU guidance on minors’ online protection explicitly references effective age assurance methods and points to the EU Digital Identity Wallet ecosystem and interim “blueprint” solutions as compliance examples—while also emphasising that methods should be accurate, reliable, robust, non-intrusive, and non-discriminatory.
The EU’s digital identity programme is also on a concrete timeline. EU policy materials state that Regulation (EU) 2024/1183 establishing the European Digital Identity Framework has entered into force and that Member States are mandated to provide EU Digital Identity wallets to citizens by the end of 2026.
The GDPR, adopted by the European Parliament, consists of 11 chapters that cover various aspects of data protection, including general provisions, principles, and rights of data subjects. The European Parliament continues to play a central role in shaping and updating data protection legislation across the EU.
What’s most important, strategically, is that EU documentation for the wallet age verification use case is already structured around selective disclosure and cryptographic proof: prove the threshold, avoid revealing excess identity data, and reduce breach impact by storing less. That is not just good privacy practice—it is quickly becoming the reference model regulators will recognise as “state of the art.”
For platforms, the implication is straightforward: build now in a way that can accept interoperable proof-of-age credentials later. If you design age verification as identity ingestion, migration will be painful. If you design it as a minimised eligibility claim with strong separation and short retention, you’re far closer to where EU regulatory tooling is headed.
Public authorities, except when acting in a judicial capacity, are subject to specific GDPR obligations, including the requirement to appoint a Data Protection Officer. This highlights the regulation's focus on accountability for large-scale data processing by government bodies.
Comparatively, while the EU has established comprehensive data protection and age verification standards through the GDPR, developments at the federal level in other countries, such as the United States, are ongoing, with federal legislation being considered to address online safety and privacy.
The compliance endgame is not “perfect certainty at any cost.” It is effective protection for minors with the least intrusive, privacy-preserving method that still works—and a governance posture that can prove you made those trade-offs deliberately.
Want to learn more?
Explore our other articles and stay up to date with the latest in age verification and compliance.
Browse all articles